Why Is Experian Asking For My Money After Losing My Social Security Number?
Some of the recent breaches that hit Anthem and Experian are worst case scenarios for consumers. In these cases, your core personal information (SSN, maiden name, previous addresses, etc.) are already housed at these two companies even if you did not explicitly directly give them this information. Events that require verifying your identity and checking your credit will passthrough this personal information from the company you are doing business with to one of many entities. When consumer data at these companies gets compromised, it makes it trivial to apply for credit cards in your name, or do even more nefarious actions such as claim your tax refund. Hijacking accounts and impersonation also become easier. Armed with a SSN, maiden name, driver's license, and birthday, a criminal can grab a few other puzzle pieces (volunteered or not) online (past addresses, high school or college attended) to blow through typical password recovery questions:
- What is your high school mascot?
- What is your mother's maiden name?
- Which of these streets have you lived on in the last 5 years?
When the potential victim has high value, mix the above with a little sweet talk on the phone with a service representative. This is why I highly recommend using the most unique security question available to you and using non-standard answers to these types of security questions (you can make up anything you want so long as you remember it or have it recorded in a password manager application).
More concerning than the data breaches, are the current protocols and incentives for the companies responsible for them, which leads me to the title of this blog post...
Why Is Experian Asking for my Money After Losing my Social Security Number?
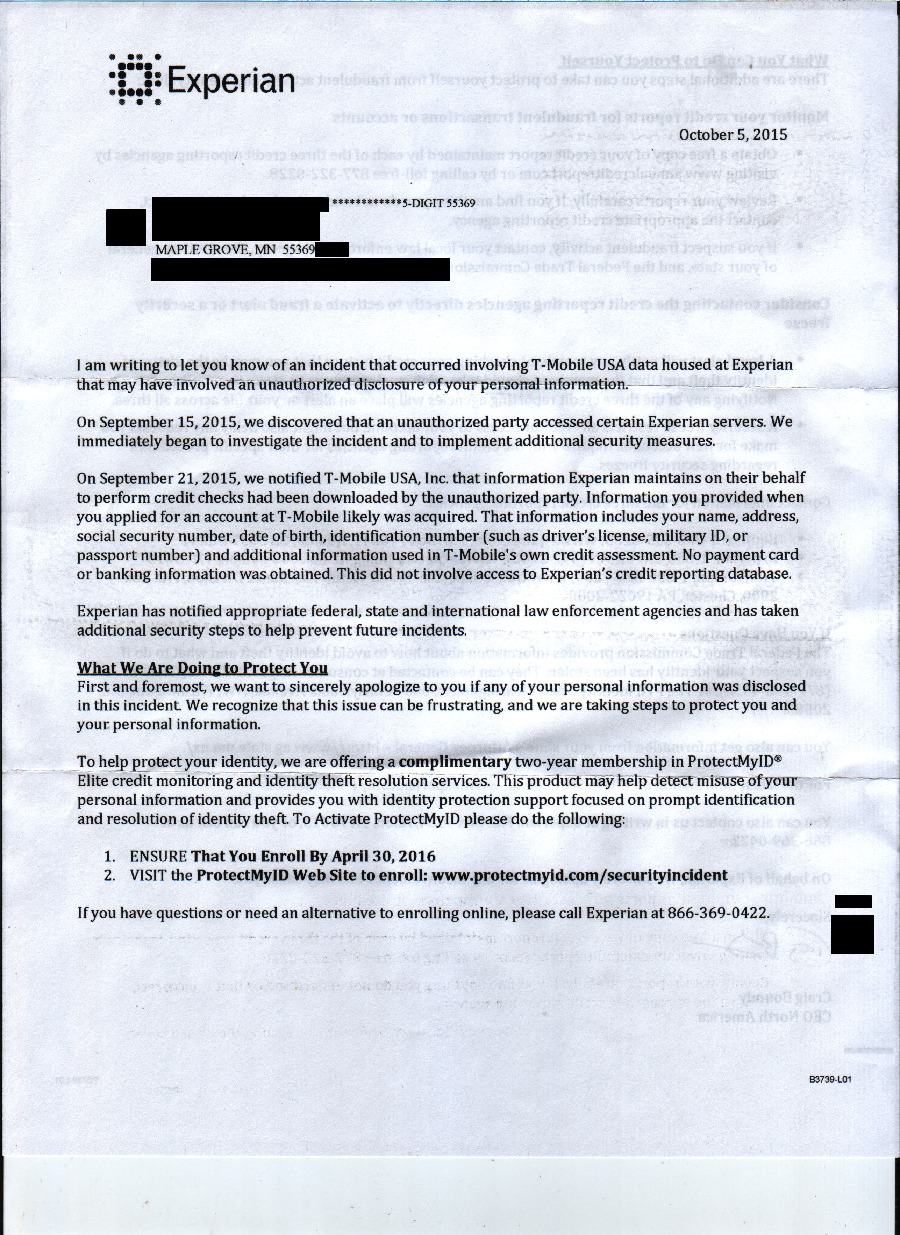
I would not expect McDonald's to offer me a year of free hamburgers (converting into a paid subscription for suspect hamburgers the following year) as compensation if they served me a hamburger that gave me a lifelong bacterial infection. Yet apparently this is essentially what Experian CEO Craig Boundy suggests in his letter sent out to affected customers:

We are first greeted with a rather haphazard attempt to describe exactly what information was compromised and what the ramifications are (perhaps too grave for them to admit). Craig goes on to subtly imply that because no payment card or banking information was compromised, this breach may not be the complete disaster that it most certainly is. I'll trade my credit card being compromised instead of my SSN and license in a heartbeat. I can talk to my bank directly and typically remedy the situation in a matter of minutes.
In a bold move after this half apology, he immediately promotes Experian's own monitoring services as a response to the breach. This should make you scratch your head for a couple reasons:
- ID theft monitoring only provides a notification once someone has attempted and possibly stolen your identity or money. It is reactive, not proactive. If you want to test this, call Experian and ask for a written guarantee your identity won't be stolen with this service and report back here if you hear differently. What Experian is offering is a monitoring service with insurance for disaster recovery provided by AIG. The insurance component might be useful, but unless the typical insurance claim process makes you feel warm and fuzzy inside, don't consider this a panacea.
- You only receive this band-aid solution for 2 years, after which you would have to pay $200/yr for it. Seems like a conflict of interest to me. Shouldn't Experian have to pay for an independent 3rd party service and not offer their own? At the minimum, Experian should be forced to provide this complimentary service indefinitely. Are copies of my comprised information magically removed from the internet after 2 years?
Worse yet, Experian buries the most effective protections (the security fraud alert and credit freeze) on the back of the letter and provides little information regarding its effectiveness.
This hints again at another conflict of interest. The fraud alert and credit freeze ultimately costs Experian money. The fraud alert will require them to have extra verification steps completed, presumably by a paid human on the phone, to verify any new credit events. Likewise, placing a credit freeze will prevent Experian from conducting business with 3rd party companies and, perhaps more concerning for them, this business could go to other credit bureaus. With this context, the motives behind the order of options offered in the 'apology' letter reveals itself.
The extra verification steps resulting from starting fraud alerts and credit freezes are entirely worth it in my opinion. How often do you get a new car loan, mortgage, or credit card? Certainly not daily. These are predictable events and prior to these events you can remove or 'thaw' your credit freeze (whatever 'thawing' fees you are charged are less than a beer at the bar or a month of Netflix). To do this effectively, simply ask the business you are working with the name of the bureau they partner with for credit verification and what your options are. Then 'thaw' your credit freeze temporarily at the specific bureau. Frankly, these minor extra hoops required for verification seem like something I would want 'enabled' all the time (controls impulse credit consumption and prevents most identity theft)! I plan on renewing my fraud alerts indefinitely.
So what are some actions the government can immediately take to help data breach victims manage all the work we did in part 1 of this blog post? Continue to part 3 of this blog post.
